动手验证电信DNS劫持对RBL的影响
出处:blog.chinaunix.net 作者:Glen Tang 时间:2007-3-14 19:01:02
前段时间梭子鱼防火墙的RBL判断出现异常,它将所有的IP(白名单IP除外)都判断成在黑名单内,我们使用的是sbl.spamhaus.org和xbl.spamhaus.org。起初怀疑是其服务出现问题,后来恰逢DNS根域服务器遭受攻击,都以为是根域服务器的影响,就暂时停用了rbl功能。但最近发现垃圾邮件量有所增加,和梭子鱼售后工程师联系后,告知是电信dns劫持的原因。更换为未被劫持的DNS后问题解决。由于一直对rbl的工作原理理解不是特别透彻,所以决心搞清楚一下到底是怎么影响的。
一、RBL的工作原理:据http://www.anti-spam.org.cn/refe ... ction=Show&ID=1的描述,rbl工作步骤为:
一、RBL的工作原理:据http://www.anti-spam.org.cn/refe ... ction=Show&ID=1的描述,rbl工作步骤为:
QUOTE:
如果要判断一个地址11.22.33.44是否被列入了黑名单,那么使用黑名单服务的软件会发出一个DNS查询到黑名单服务器(如cbl.anti-spam.org.cn),该查询是这样的:查找 44.33.22.11.cbl.anti-spam.org.cn 是否存在A记录?如果该地址被列入了黑名单,那么服务器会返回一个有效地址的答案。按照惯例,这个地址是127.0.0.0/8内的地址如127.0.0.2(之所以使用这个地址是因为127/8这个地址段被保留用于打环测试,除了127.0.0.1用于打环地址,其它的地址都可以被用来做这个使用,比如有时候还用127.0.0.3等。)。如果没有列入黑名单,那么查询会得到一个否定回答(NXDOMAIN)。
里面有个关键问题(红色字体):
1、rbl查询的结果是一定要在127.0.0.0/8内吗?如果返回来一个有效的internet地址会怎样(DNS劫持发生时)?
另外增加几个需要弄清楚的问题:
2、电信劫持dns的行为,在什么情况下才会发生?
3、劫持的目的IP是什么?IP的属主是谁?
二、资源需求
首先需要这样一些资源:
怀疑被劫持的DNS IP: 202.96.209.6
未被劫持的DNS IP: 202.96.199.133
在xbl.spamhaus.org或sbl.spamhaus.org的RBL内的IP: 61.83.209.40
不在xbl.spamhaus.org或sbl.spamhaus.org的RBL内的IP: 219.239.89.18,211.150.96.22
对正常域名的解析: www.163.com
三、开始对比验证:由于windows的nslookup使用不太方便,所以在linux主机上使用dig,host等命令来查询。
1、 在未被劫持的DNS上,对RBL内的IP做RBL查询,正常情况下应该返回127.0.0.0/8内的地址:
1、rbl查询的结果是一定要在127.0.0.0/8内吗?如果返回来一个有效的internet地址会怎样(DNS劫持发生时)?
另外增加几个需要弄清楚的问题:
2、电信劫持dns的行为,在什么情况下才会发生?
3、劫持的目的IP是什么?IP的属主是谁?
二、资源需求
首先需要这样一些资源:
怀疑被劫持的DNS IP: 202.96.209.6
未被劫持的DNS IP: 202.96.199.133
在xbl.spamhaus.org或sbl.spamhaus.org的RBL内的IP: 61.83.209.40
不在xbl.spamhaus.org或sbl.spamhaus.org的RBL内的IP: 219.239.89.18,211.150.96.22
对正常域名的解析: www.163.com
三、开始对比验证:由于windows的nslookup使用不太方便,所以在linux主机上使用dig,host等命令来查询。
1、 在未被劫持的DNS上,对RBL内的IP做RBL查询,正常情况下应该返回127.0.0.0/8内的地址:
QUOTE:
[root@mailtest2 tmp]# cat /etc/resolv.conf
nameserver 202.96.199.133
[root@mailtest2 tmp]# host 40.209.83.61.xbl.spamhaus.org
40.209.83.61.xbl.spamhaus.org has address 127.0.0.4
[root@mailtest2 tmp]# dig @202.96.199.133 40.209.83.61.xbl.spamhaus.org
………………………… #省略部分输出
;; QUESTION SECTION:
;40.209.83.61.xbl.spamhaus.org. IN A
;; ANSWER SECTION:
40.209.83.61.xbl.spamhaus.org. 1758 IN A 127.0.0.4
………………………… #省略部分输出
;; Query time: 10 msec
;; SERVER: 202.96.199.133#53(202.96.199.133)
;; WHEN: Wed Feb 28 11:42:34 2007
;; MSG SIZE rcvd: 466
nameserver 202.96.199.133
[root@mailtest2 tmp]# host 40.209.83.61.xbl.spamhaus.org
40.209.83.61.xbl.spamhaus.org has address 127.0.0.4
[root@mailtest2 tmp]# dig @202.96.199.133 40.209.83.61.xbl.spamhaus.org
………………………… #省略部分输出
;; QUESTION SECTION:
;40.209.83.61.xbl.spamhaus.org. IN A
;; ANSWER SECTION:
40.209.83.61.xbl.spamhaus.org. 1758 IN A 127.0.0.4
………………………… #省略部分输出
;; Query time: 10 msec
;; SERVER: 202.96.199.133#53(202.96.199.133)
;; WHEN: Wed Feb 28 11:42:34 2007
;; MSG SIZE rcvd: 466
返回值正常。
2、 在未被劫持的DNS上,对不在RBL内的IP做RBL查询,正常情况下应该返回NXDOMAIN;
2、 在未被劫持的DNS上,对不在RBL内的IP做RBL查询,正常情况下应该返回NXDOMAIN;
QUOTE:
[root@mailtest2 tmp]# cat /etc/resolv.conf
nameserver 202.96.199.133
[root@mailtest2 tmp]# host 18.89.239.219.xbl.spamhaus.org
Host 18.89.239.219.xbl.spamhaus.org not found: 3(NXDOMAIN)
[root@mailtest2 tmp]# dig @202.96.199.133 18.89.239.219.xbl.spamhaus.org
; <<>> DiG 9.2.4rc6 <<>> @202.96.199.133 18.89.239.219.xbl.spamhaus.org
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NXDOMAIN, id: 48464
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 0
;; QUESTION SECTION:
;18.89.239.219.xbl.spamhaus.org. IN A
;; AUTHORITY SECTION:
xbl.spamhaus.org. 878 IN SOA need.to.know.only. hostmaster.spamhaus.org. 2007022814 3600 600 432000 900
;; Query time: 21 msec
;; SERVER: 202.96.199.133#53(202.96.199.133)
;; WHEN: Wed Feb 28 11:53:36 2007
;; MSG SIZE rcvd: 112
[root@mailtest2 tmp]# host 22.96.150.211.xbl.spamhaus.org
Host 22.96.150.211.xbl.spamhaus.org not found: 3(NXDOMAIN)
[root@mailtest2 tmp]# dig @202.96.199.133 22.96.150.211.xbl.spamhaus.org
; <<>> DiG 9.2.4rc6 <<>> @202.96.199.133 22.96.150.211.xbl.spamhaus.org
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NXDOMAIN, id: 27365
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 0
;; QUESTION SECTION:
;22.96.150.211.xbl.spamhaus.org. IN A
;; AUTHORITY SECTION:
xbl.spamhaus.org. 878 IN SOA need.to.know.only. hostmaster.spamhaus.org. 2007022823 3600 600 432000 900
;; Query time: 39 msec
;; SERVER: 202.96.199.133#53(202.96.199.133)
;; WHEN: Wed Feb 28 14:13:06 2007
;; MSG SIZE rcvd: 112
nameserver 202.96.199.133
[root@mailtest2 tmp]# host 18.89.239.219.xbl.spamhaus.org
Host 18.89.239.219.xbl.spamhaus.org not found: 3(NXDOMAIN)
[root@mailtest2 tmp]# dig @202.96.199.133 18.89.239.219.xbl.spamhaus.org
; <<>> DiG 9.2.4rc6 <<>> @202.96.199.133 18.89.239.219.xbl.spamhaus.org
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NXDOMAIN, id: 48464
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 0
;; QUESTION SECTION:
;18.89.239.219.xbl.spamhaus.org. IN A
;; AUTHORITY SECTION:
xbl.spamhaus.org. 878 IN SOA need.to.know.only. hostmaster.spamhaus.org. 2007022814 3600 600 432000 900
;; Query time: 21 msec
;; SERVER: 202.96.199.133#53(202.96.199.133)
;; WHEN: Wed Feb 28 11:53:36 2007
;; MSG SIZE rcvd: 112
[root@mailtest2 tmp]# host 22.96.150.211.xbl.spamhaus.org
Host 22.96.150.211.xbl.spamhaus.org not found: 3(NXDOMAIN)
[root@mailtest2 tmp]# dig @202.96.199.133 22.96.150.211.xbl.spamhaus.org
; <<>> DiG 9.2.4rc6 <<>> @202.96.199.133 22.96.150.211.xbl.spamhaus.org
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NXDOMAIN, id: 27365
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 0
;; QUESTION SECTION:
;22.96.150.211.xbl.spamhaus.org. IN A
;; AUTHORITY SECTION:
xbl.spamhaus.org. 878 IN SOA need.to.know.only. hostmaster.spamhaus.org. 2007022823 3600 600 432000 900
;; Query time: 39 msec
;; SERVER: 202.96.199.133#53(202.96.199.133)
;; WHEN: Wed Feb 28 14:13:06 2007
;; MSG SIZE rcvd: 112
返回正常。
3、 在未被劫持的DNS上,解析正常域名:
3、 在未被劫持的DNS上,解析正常域名:
QUOTE:
[root@mailtest2 tmp]# cat /etc/resolv.conf
nameserver 202.96.199.133
[root@mailtest2 tmp]# host www.163.com
www.163.com is an alias for www.cache.split.netease.com.
www.cache.split.netease.com has address 220.181.31.184
www.cache.split.netease.com has address 220.181.28.50
www.cache.split.netease.com has address 220.181.28.51
www.cache.split.netease.com has address 220.181.28.52
www.cache.split.netease.com has address 220.181.28.53
www.cache.split.netease.com has address 220.181.28.54
www.cache.split.netease.com has address 220.181.31.182
www.cache.split.netease.com has address 220.181.31.183
[root@mailtest2 tmp]# dig @202.96.199.133 www.163.com
………………………… #省略部分输出
;; QUESTION SECTION:
;www.163.com. IN A
;; ANSWER SECTION:
www.163.com. 11544 IN CNAME www.cache.split.netease.com.
www.cache.split.netease.com. 296 IN A 220.181.28.50
www.cache.split.netease.com. 296 IN A 220.181.28.51
www.cache.split.netease.com. 296 IN A 220.181.28.52
www.cache.split.netease.com. 296 IN A 220.181.28.53
www.cache.split.netease.com. 296 IN A 220.181.28.54
www.cache.split.netease.com. 296 IN A 220.181.31.182
www.cache.split.netease.com. 296 IN A 220.181.31.183
www.cache.split.netease.com. 296 IN A 220.181.31.184
………………………… #省略部分输出
;; Query time: 6 msec
;; SERVER: 202.96.199.133#53(202.96.199.133)
;; WHEN: Wed Feb 28 11:58:23 2007
;; MSG SIZE rcvd: 127
nameserver 202.96.199.133
[root@mailtest2 tmp]# host www.163.com
www.163.com is an alias for www.cache.split.netease.com.
www.cache.split.netease.com has address 220.181.31.184
www.cache.split.netease.com has address 220.181.28.50
www.cache.split.netease.com has address 220.181.28.51
www.cache.split.netease.com has address 220.181.28.52
www.cache.split.netease.com has address 220.181.28.53
www.cache.split.netease.com has address 220.181.28.54
www.cache.split.netease.com has address 220.181.31.182
www.cache.split.netease.com has address 220.181.31.183
[root@mailtest2 tmp]# dig @202.96.199.133 www.163.com
………………………… #省略部分输出
;; QUESTION SECTION:
;www.163.com. IN A
;; ANSWER SECTION:
www.163.com. 11544 IN CNAME www.cache.split.netease.com.
www.cache.split.netease.com. 296 IN A 220.181.28.50
www.cache.split.netease.com. 296 IN A 220.181.28.51
www.cache.split.netease.com. 296 IN A 220.181.28.52
www.cache.split.netease.com. 296 IN A 220.181.28.53
www.cache.split.netease.com. 296 IN A 220.181.28.54
www.cache.split.netease.com. 296 IN A 220.181.31.182
www.cache.split.netease.com. 296 IN A 220.181.31.183
www.cache.split.netease.com. 296 IN A 220.181.31.184
………………………… #省略部分输出
;; Query time: 6 msec
;; SERVER: 202.96.199.133#53(202.96.199.133)
;; WHEN: Wed Feb 28 11:58:23 2007
;; MSG SIZE rcvd: 127
返回值正常。
4、 在怀疑被劫持的DNS上,对RBL内的IP做RBL查询,正常情况下应该返回127.0.0.0/8内的地址:
[/quote]
[root@mailtest2 tmp]# cat /etc/resolv.conf
nameserver 202.96.209.6
[root@mailtest2 tmp]# host 40.209.83.61.xbl.spamhaus.org
40.209.83.61.xbl.spamhaus.org has address 127.0.0.4
[root@mailtest2 tmp]# dig @202.96.209.6 40.209.83.61.xbl.spamhaus.org
………………………… #省略部分输出
;; QUESTION SECTION:
;40.209.83.61.xbl.spamhaus.org. IN A
;; ANSWER SECTION:
40.209.83.61.xbl.spamhaus.org. 839 IN A 127.0.0.4
………………………… #省略部分输出
;; Query time: 7 msec
;; SERVER: 202.96.209.6#53(202.96.209.6)
;; WHEN: Wed Feb 28 13:35:13 2007
;; MSG SIZE rcvd: 466
[/quote]
返回正常。
5、 在怀疑被劫持的DNS上,对不在RBL内的IP做RBL查询,正常情况下应该返回NXDOMAIN;重点就在这个地方了
4、 在怀疑被劫持的DNS上,对RBL内的IP做RBL查询,正常情况下应该返回127.0.0.0/8内的地址:
[/quote]
[root@mailtest2 tmp]# cat /etc/resolv.conf
nameserver 202.96.209.6
[root@mailtest2 tmp]# host 40.209.83.61.xbl.spamhaus.org
40.209.83.61.xbl.spamhaus.org has address 127.0.0.4
[root@mailtest2 tmp]# dig @202.96.209.6 40.209.83.61.xbl.spamhaus.org
………………………… #省略部分输出
;; QUESTION SECTION:
;40.209.83.61.xbl.spamhaus.org. IN A
;; ANSWER SECTION:
40.209.83.61.xbl.spamhaus.org. 839 IN A 127.0.0.4
………………………… #省略部分输出
;; Query time: 7 msec
;; SERVER: 202.96.209.6#53(202.96.209.6)
;; WHEN: Wed Feb 28 13:35:13 2007
;; MSG SIZE rcvd: 466
[/quote]
返回正常。
5、 在怀疑被劫持的DNS上,对不在RBL内的IP做RBL查询,正常情况下应该返回NXDOMAIN;重点就在这个地方了
QUOTE:
[root@mailtest2 tmp]# host 18.89.239.219.xbl.spamhaus.org
18.89.239.219.xbl.spamhaus.org has address 218.83.175.154
[root@mailtest2 tmp]# dig @202.96.209.6 18.89.239.219.xbl.spamhaus.org
; <<>> DiG 9.2.4rc6 <<>> @202.96.209.6 18.89.239.219.xbl.spamhaus.org
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 54440
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;18.89.239.219.xbl.spamhaus.org. IN A
;; ANSWER SECTION:
18.89.239.219.xbl.spamhaus.org. 1800 IN A 218.83.175.154
;; Query time: 539 msec
;; SERVER: 202.96.209.6#53(202.96.209.6)
;; WHEN: Wed Feb 28 14:14:43 2007
;; MSG SIZE rcvd: 64
[root@mailtest2 tmp]# host 22.96.150.211.xbl.spamhaus.org
22.96.150.211.xbl.spamhaus.org has address 218.83.175.154
[root@mailtest2 tmp]# dig @202.96.209.6 22.96.150.211.xbl.spamhaus.org
; <<>> DiG 9.2.4rc6 <<>> @202.96.209.6 22.96.150.211.xbl.spamhaus.org
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 21397
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;22.96.150.211.xbl.spamhaus.org. IN A
;; ANSWER SECTION:
22.96.150.211.xbl.spamhaus.org. 1800 IN A 218.83.175.154
;; Query time: 831 msec
;; SERVER: 202.96.209.6#53(202.96.209.6)
;; WHEN: Wed Feb 28 14:16:24 2007
;; MSG SIZE rcvd: 64
18.89.239.219.xbl.spamhaus.org has address 218.83.175.154
[root@mailtest2 tmp]# dig @202.96.209.6 18.89.239.219.xbl.spamhaus.org
; <<>> DiG 9.2.4rc6 <<>> @202.96.209.6 18.89.239.219.xbl.spamhaus.org
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 54440
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;18.89.239.219.xbl.spamhaus.org. IN A
;; ANSWER SECTION:
18.89.239.219.xbl.spamhaus.org. 1800 IN A 218.83.175.154
;; Query time: 539 msec
;; SERVER: 202.96.209.6#53(202.96.209.6)
;; WHEN: Wed Feb 28 14:14:43 2007
;; MSG SIZE rcvd: 64
[root@mailtest2 tmp]# host 22.96.150.211.xbl.spamhaus.org
22.96.150.211.xbl.spamhaus.org has address 218.83.175.154
[root@mailtest2 tmp]# dig @202.96.209.6 22.96.150.211.xbl.spamhaus.org
; <<>> DiG 9.2.4rc6 <<>> @202.96.209.6 22.96.150.211.xbl.spamhaus.org
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 21397
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;22.96.150.211.xbl.spamhaus.org. IN A
;; ANSWER SECTION:
22.96.150.211.xbl.spamhaus.org. 1800 IN A 218.83.175.154
;; Query time: 831 msec
;; SERVER: 202.96.209.6#53(202.96.209.6)
;; WHEN: Wed Feb 28 14:16:24 2007
;; MSG SIZE rcvd: 64
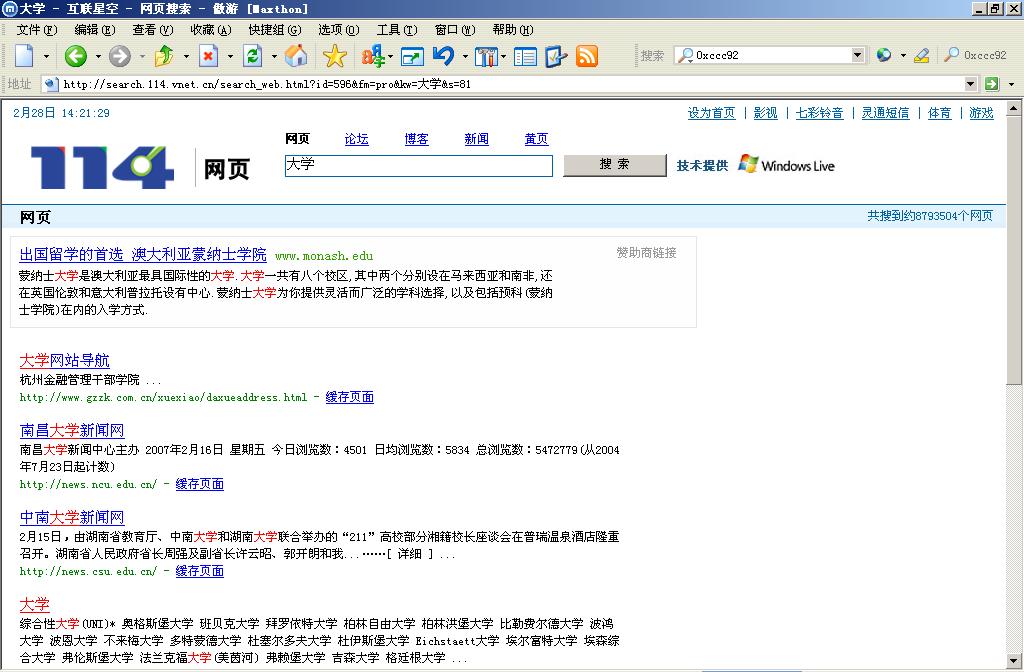
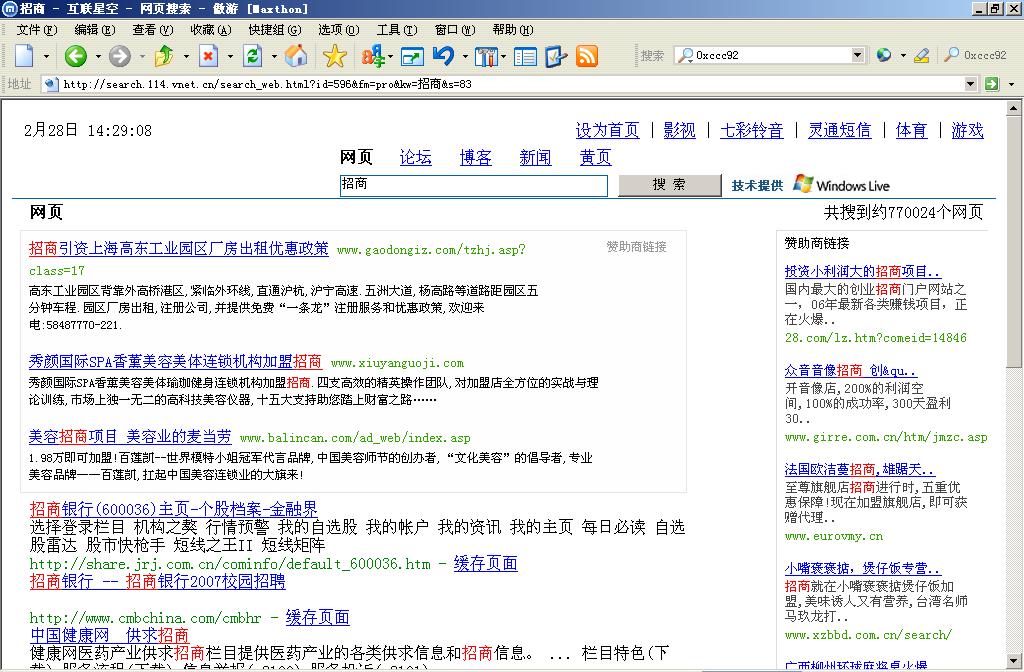
怪了,怎么解析出来一个正常IP了?把这个IP输入到IE地址栏,打开了这个网页:
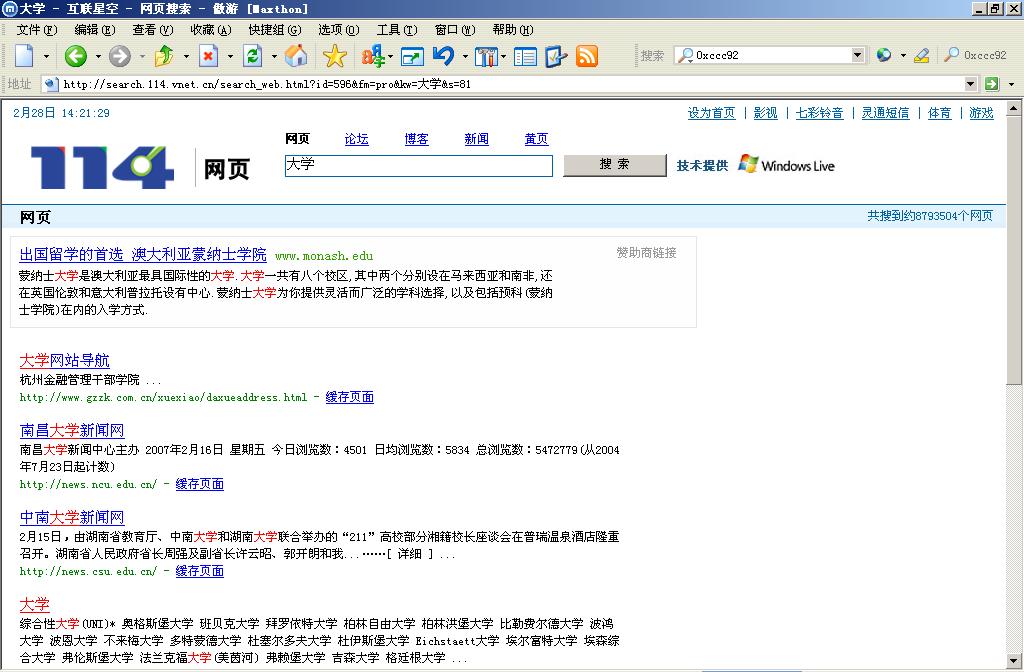
而且再开一个窗口再打开一次,页面又会变化!
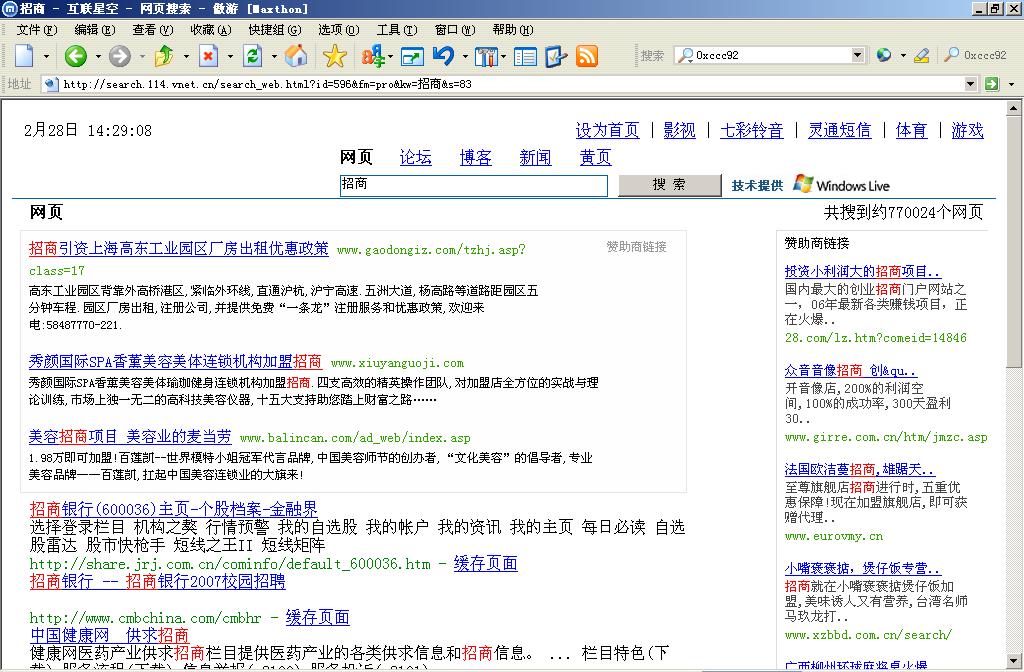
6、 在怀疑被劫持的DNS上解析一个正常的域名:
而且再开一个窗口再打开一次,页面又会变化!
6、 在怀疑被劫持的DNS上解析一个正常的域名:
QUOTE:
[root@mailtest2 tmp]# dig www.163.com
; <<>> DiG 9.2.4rc6 <<>> www.163.com
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 28059
;; flags: qr rd ra; QUERY: 1, ANSWER: 9, AUTHORITY: 2, ADDITIONAL: 2
;; QUESTION SECTION:
;www.163.com. IN A
;; ANSWER SECTION:
www.163.com. 11544 IN CNAME www.cache.split.netease.com.
www.cache.split.netease.com. 296 IN A 220.181.28.50
www.cache.split.netease.com. 296 IN A 220.181.28.51
www.cache.split.netease.com. 296 IN A 220.181.28.52
www.cache.split.netease.com. 296 IN A 220.181.28.53
www.cache.split.netease.com. 296 IN A 220.181.28.54
www.cache.split.netease.com. 296 IN A 220.181.31.182
www.cache.split.netease.com. 296 IN A 220.181.31.183
www.cache.split.netease.com. 296 IN A 220.181.31.184
;; AUTHORITY SECTION:
split.netease.com. 1196 IN NS ns-split1.netease.com.
split.netease.com. 1196 IN NS ns-split2.netease.com.
;; ADDITIONAL SECTION:
ns-split1.netease.com. 6260 IN A 202.106.168.79
ns-split2.netease.com. 5748 IN A 220.181.28.4
;; Query time: 6 msec
;; SERVER: 202.96.209.6#53(202.96.209.6)
;; WHEN: Fri Mar 2 10:17:55 2007
;; MSG SIZE rcvd: 275
; <<>> DiG 9.2.4rc6 <<>> www.163.com
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 28059
;; flags: qr rd ra; QUERY: 1, ANSWER: 9, AUTHORITY: 2, ADDITIONAL: 2
;; QUESTION SECTION:
;www.163.com. IN A
;; ANSWER SECTION:
www.163.com. 11544 IN CNAME www.cache.split.netease.com.
www.cache.split.netease.com. 296 IN A 220.181.28.50
www.cache.split.netease.com. 296 IN A 220.181.28.51
www.cache.split.netease.com. 296 IN A 220.181.28.52
www.cache.split.netease.com. 296 IN A 220.181.28.53
www.cache.split.netease.com. 296 IN A 220.181.28.54
www.cache.split.netease.com. 296 IN A 220.181.31.182
www.cache.split.netease.com. 296 IN A 220.181.31.183
www.cache.split.netease.com. 296 IN A 220.181.31.184
;; AUTHORITY SECTION:
split.netease.com. 1196 IN NS ns-split1.netease.com.
split.netease.com. 1196 IN NS ns-split2.netease.com.
;; ADDITIONAL SECTION:
ns-split1.netease.com. 6260 IN A 202.106.168.79
ns-split2.netease.com. 5748 IN A 220.181.28.4
;; Query time: 6 msec
;; SERVER: 202.96.209.6#53(202.96.209.6)
;; WHEN: Fri Mar 2 10:17:55 2007
;; MSG SIZE rcvd: 275
解析正常;难道这个DNS把所有解析不到的域名都劫持到218.83.175.154?下面验证一下:
7、 在怀疑被劫持的DNS上解析一个伪造的域名:
7、 在怀疑被劫持的DNS上解析一个伪造的域名:
QUOTE:
[root@mailtest2 tmp]# dig @202.96.209.6 false.163.com
; <<>> DiG 9.2.4rc6 <<>> @202.96.209.6 false.163.com
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 37904
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;false.163.com. IN A
;; ANSWER SECTION:
false.163.com. 1800 IN A 218.83.175.154
;; Query time: 263 msec
;; SERVER: 202.96.209.6#53(202.96.209.6)
;; WHEN: Wed Feb 28 14:33:41 2007
;; MSG SIZE rcvd: 47
; <<>> DiG 9.2.4rc6 <<>> @202.96.209.6 false.163.com
;; global options: printcmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 37904
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;false.163.com. IN A
;; ANSWER SECTION:
false.163.com. 1800 IN A 218.83.175.154
;; Query time: 263 msec
;; SERVER: 202.96.209.6#53(202.96.209.6)
;; WHEN: Wed Feb 28 14:33:41 2007
;; MSG SIZE rcvd: 47
8、 218.83.175.154这个IP是谁的?
QUOTE:
[root@mailtest2 tmp]# whois 218.83.175.154
[Querying whois.apnic.net]
[whois.apnic.net]
% [whois.apnic.net node-1]
% Whois data copyright terms http://www.apnic.net/db/dbcopyright.html
inetnum: 218.78.0.0 - 218.83.255.255
netname: CHINANET-SH
descr: CHINANET Shanghai province network
descr: Data Communication Division
descr: China Telecom
country: CN
admin-c: CH93-AP
tech-c: XI5-AP
mnt-by: APNIC-HM
mnt-lower: MAINT-CHINANET-SH
mnt-routes: MAINT-CHINANET-SH
status: ALLOCATED PORTABLE
changed: hm-changed@apnic.net 20060427
source: APNIC
person: Chinanet Hostmaster
nic-hdl: CH93-AP
e-mail: anti-spam@ns.chinanet.cn.net
address: No.31 ,jingrong street,beijing
address: 100032
phone: +86-10-58501724
fax-no: +86-10-58501724
country: CN
changed: lqing@chinatelecom.com.cn 20051212
mnt-by: MAINT-CHINANET
source: APNIC
person: Wu Xiao Li
address: Room 805,61 North Si Chuan Road,Shanghai,200085,PRC
country: CN
phone: +86-21-63630562
fax-no: +86-21-63630566
e-mail: ip-admin@mail.online.sh.cn
nic-hdl: XI5-AP
mnt-by: MAINT-CHINANET-SH
changed: ip-admin@mail.online.sh.cn 20010510
source: APNIC
[Querying whois.apnic.net]
[whois.apnic.net]
% [whois.apnic.net node-1]
% Whois data copyright terms http://www.apnic.net/db/dbcopyright.html
inetnum: 218.78.0.0 - 218.83.255.255
netname: CHINANET-SH
descr: CHINANET Shanghai province network
descr: Data Communication Division
descr: China Telecom
country: CN
admin-c: CH93-AP
tech-c: XI5-AP
mnt-by: APNIC-HM
mnt-lower: MAINT-CHINANET-SH
mnt-routes: MAINT-CHINANET-SH
status: ALLOCATED PORTABLE
changed: hm-changed@apnic.net 20060427
source: APNIC
person: Chinanet Hostmaster
nic-hdl: CH93-AP
e-mail: anti-spam@ns.chinanet.cn.net
address: No.31 ,jingrong street,beijing
address: 100032
phone: +86-10-58501724
fax-no: +86-10-58501724
country: CN
changed: lqing@chinatelecom.com.cn 20051212
mnt-by: MAINT-CHINANET
source: APNIC
person: Wu Xiao Li
address: Room 805,61 North Si Chuan Road,Shanghai,200085,PRC
country: CN
phone: +86-21-63630562
fax-no: +86-21-63630566
e-mail: ip-admin@mail.online.sh.cn
nic-hdl: XI5-AP
mnt-by: MAINT-CHINANET-SH
changed: ip-admin@mail.online.sh.cn 20010510
source: APNIC
IP属于中国电信,显然重定向出来的网页也属于中国电信…………
四、总结:
可以得出结论:可恶的电信在其部分DNS上设置了规则:所有解析不到的域名,都返回218.83.175.154这个IP
五、电信的DNS劫持行为,怎样影响到RBL的?
显而易见,所有解析不到的域名,都有返回值。虽然不是127.0.0.0/8网段,但是我的梭子鱼放火墙显然没有理会其中的内容,所以自然而然把所有的IP都判断为黑名单了(因为没有收到(NXDOMAIN))!
四、总结:
可以得出结论:可恶的电信在其部分DNS上设置了规则:所有解析不到的域名,都返回218.83.175.154这个IP
五、电信的DNS劫持行为,怎样影响到RBL的?
显而易见,所有解析不到的域名,都有返回值。虽然不是127.0.0.0/8网段,但是我的梭子鱼放火墙显然没有理会其中的内容,所以自然而然把所有的IP都判断为黑名单了(因为没有收到(NXDOMAIN))!
| 自由广告区 |
| 分类导航 |
| 邮件新闻资讯: IT业界 | 邮件服务器 | 邮件趣闻 | 移动电邮 电子邮箱 | 反垃圾邮件|邮件客户端|网络安全 行业数据 | 邮件人物 | 网站公告 | 行业法规 网络技术: 邮件原理 | 网络协议 | 网络管理 | 传输介质 线路接入 | 路由接口 | 邮件存储 | 华为3Com CISCO技术 | 网络与服务器硬件 操作系统: Windows 9X | Linux&Uinx | Windows NT Windows Vista | FreeBSD | 其它操作系统 邮件服务器: 程序与开发 | Exchange | Qmail | Postfix Sendmail | MDaemon | Domino | Foxmail KerioMail | JavaMail | Winwebmail |James Merak&VisNetic | CMailServer | WinMail 金笛邮件系统 | 其它 | 反垃圾邮件: 综述| 客户端反垃圾邮件|服务器端反垃圾邮件 邮件客户端软件: Outlook | Foxmail | DreamMail| KooMail The bat | 雷鸟 | Eudora |Becky! |Pegasus IncrediMail |其它 电子邮箱: 个人邮箱 | 企业邮箱 |Gmail 移动电子邮件:服务器 | 客户端 | 技术前沿 邮件网络安全: 软件漏洞 | 安全知识 | 病毒公告 |防火墙 攻防技术 | 病毒查杀| ISA | 数字签名 邮件营销: Email营销 | 网络营销 | 营销技巧 |营销案例 邮件人才:招聘 | 职场 | 培训 | 指南 | 职场 解决方案: 邮件系统|反垃圾邮件 |安全 |移动电邮 |招标 产品评测: 邮件系统 |反垃圾邮件 |邮箱 |安全 |客户端 |